A DDoS attack (Distributed Denial of Service) is a deliberate attempt to disrupt the normal operation of a server, service, or network by overwhelming it with a massive volume of traffic. The attack is carried out using a large number of requests sent simultaneously from many different devices, making the target unavailable to legitimate users.
Types of DDoS attacks
Depending on the target and attack method, DDoS attacks are usually divided into three main categories:
-
Network-layer attacks.
These attacks aim to saturate network bandwidth or overload network devices such as routers and firewalls. -
Application-layer attacks.
These target specific applications or services (for example, web servers or APIs) by sending seemingly legitimate requests that consume significant server resources. -
Resource exhaustion attacks.
These focus on depleting critical system resources such as CPU, memory, or connection tables by generating a high number of requests or connections.
How a DDoS attack works
A DDoS attack typically begins with attackers compromising a large number of devices—computers, servers, or IoT devices—by installing malicious software on them. These infected devices form a botnet, a remotely controlled network of machines.
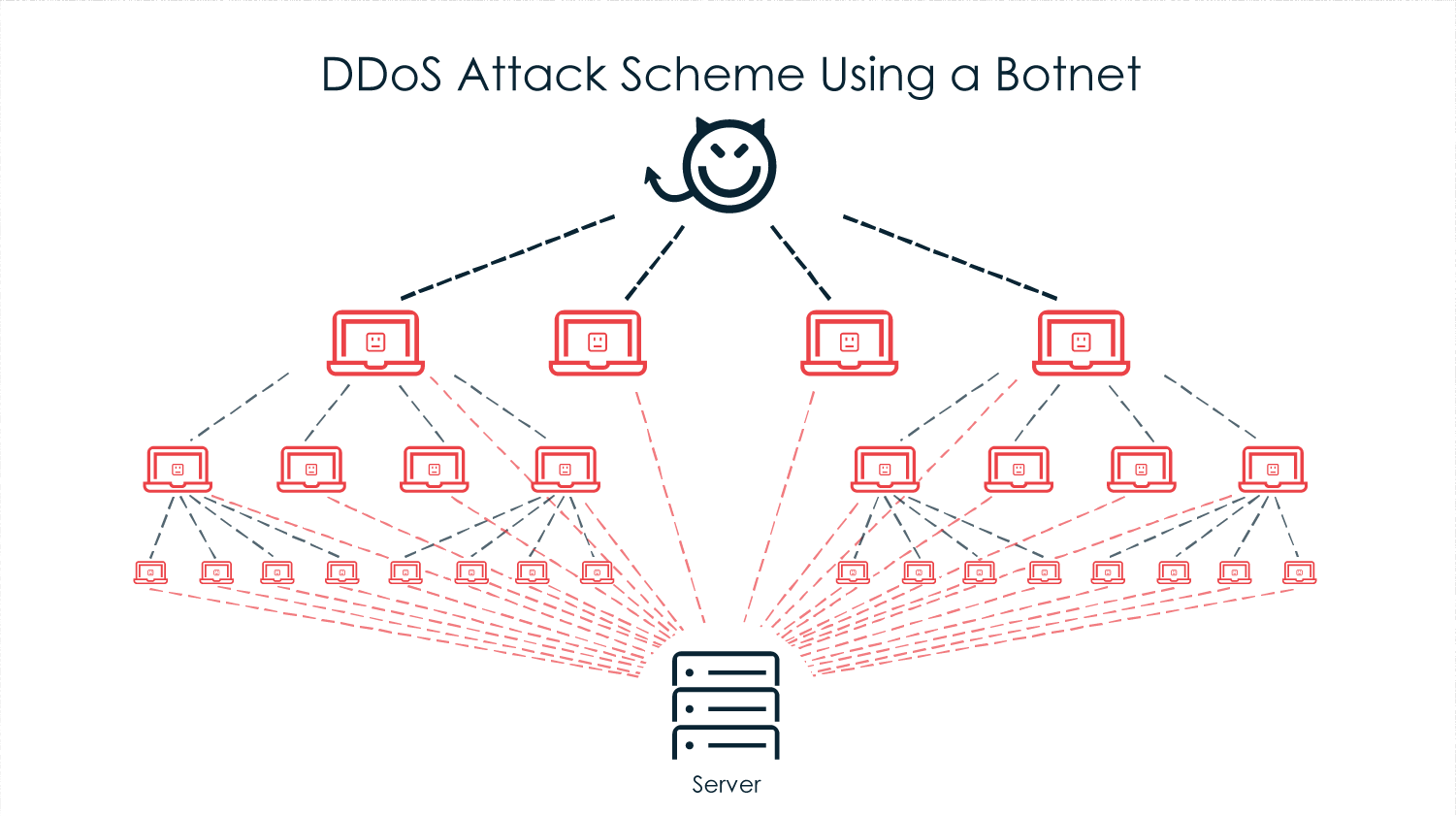
DDoS attack scheme. Image: selectel.ru
At a chosen moment, the attackers issue a command to the botnet, instructing all infected devices to simultaneously send traffic or requests to the target server or network. As a result, the target becomes overloaded, performance degrades significantly, and in many cases the service becomes partially or completely unavailable.
Goals of DDoS attacks
Attackers may launch DDoS attacks for various reasons. The most common include:
-
Sabotage — disrupting competitors’ websites or online services;
-
Extortion — demanding ransom payments in exchange for stopping the attack;
-
Political motives — protesting against governments, organizations, or their opponents;
-
Entertainment or demonstration of power — conducting attacks for personal interest or notoriety.
According to industry reports, tens of thousands of DDoS attacks occur worldwide every day. A significant portion of them are successfully mitigated thanks to modern traffic filtering, monitoring systems, and specialized DDoS protection solutions.